Quick Decision Framework
- Who This Is For: DeFi builders, protocol engineers, and blockchain security leads who understand that NIST finalized its post-quantum signature standards in 2024 and are now evaluating which tooling actually delivers production-grade quantum safety without wrecking throughput or forcing a full protocol rewrite.
- Skip If: You are building a project with a lifespan under 12 months and no long-term asset custody. The migration overhead is not worth it at that time horizon. Come back when you are managing value that will persist past the next hardware generation.
- Key Benefit: A ranked, scored comparison of five solutions that have been benchmarked on real networks, audited by third parties, and measured for throughput, so you can move from evaluation to sprint planning without reading every vendor white paper yourself.
- What You’ll Need: A current map of where your keys live today, a rough sense of your engineering team’s preferred stack (EVM, Rust, or C), and clarity on whether you need a bolt-on shield, a library swap, or a new chain foundation.
- Time to Complete: 15 minutes to read. One to two sprints to stand up a sandbox and validate your chosen approach against production traffic.
Wait too long and you inherit years of hard-fork politics, wallet migrations, and audit headaches. Move now and you turn an existential risk into a competitive edge.
What You’ll Learn
- Understand why the NIST 2024 standardization of ML-DSA and SLH-DSA changed the post-quantum conversation from theoretical to operational for every DeFi team managing long-lived assets
- Evaluate five ranked solutions across six weighted criteria including security pedigree, performance overhead, and integration friction so you can match the right tool to your stack
- Assess each solution’s real-world deployment evidence, from Solana testnet throughput numbers to Algorand’s first Falcon-secured mainnet transaction in November 2025
- Apply a comparison framework that distinguishes bolt-on shields, open-source libraries, and quantum-native chains so your team picks the right architectural path the first time
- Execute an eight-step implementation checklist that moves your upgrade from whiteboard to mainnet without stalling in testing or triggering governance conflict
Crypto moves at break-neck speed, yet its defenses still hinge on curves a quantum computer can snap like brittle glass.
In July 2024, NIST added ML-DSA (formerly Dilithium) and SLH-DSA (formerly SPHINCS+) to the FIPS catalogue—the first production-grade, quantum-safe signatures on record (NIST announcement).
That milestone flipped the script for DeFi builders. “Someday” is no longer an excuse; the standards are written, the toolkits are shipping, and attackers are already archiving public keys for a brute-force payday later. Project 11’s open-source Risq List scans the Bitcoin UTXO set each day and currently flags about 1.7 million BTC locked in early pay-to-pubkey addresses that expose their public keys at spend.
A cryptographically relevant quantum computer could sweep those coins within minutes once the signatures appear on-chain, turning the abstract harvest-now-decrypt-later threat into a concrete nine-figure price tag.
Wait too long and you inherit years of hard-fork politics, wallet migrations, and audit headaches. Move now and you turn an existential risk into a competitive edge.
We sifted through the noise—white-paper chains, buzzword blogs, and genuine breakthroughs—to spotlight five solutions that deliver. They aren’t just mathematically sound; they’ve been battle-tested on real networks, audited by third parties, and measured for throughput so your DEX or lending pool keeps humming.
The list is ranked. Security pedigree carries the most weight, followed by performance overhead and integration friction. A quick comparison table and an implementation checklist follow the deep dives, so you can jump from “interesting” to “in sprint” without slogging through vendor PDFs.
Ready? Let’s future-proof your smart contracts before a quantum adversary reverse-engineers them.
How we ranked the solutions.
Transparent scoring matters. You deserve to know exactly why one toolkit tops another, not just see a numbered list and a shrug. So we built a six-factor rubric that mirrors the real headaches you and your engineers face every release cycle.
First, we weighted security pedigree highest. A shiny feature set is pointless if a graduate student can break the math. We checked every contender for public audits, peer-reviewed cryptanalysis, and alignment with NIST’s 2024 signature standards ML-DSA and SLH-DSA, the only algorithms currently carrying a federal stamp of approval.
Next came performance overhead. DeFi thrives on speed. If a post-quantum patch drags block times or gas fees, users will flee before the next epoch. We dug through benchmark reports and live-network demos to confirm that claimed throughput survives contact with reality.
Integration friction rounded out the top three. Whether you run Solidity on EVM or Rust on Solana, you need upgrades that slot into the stack without a six-month refactor. Drop-in libraries and backward-compatible key formats scored far better than “rip-and-replace” architectures.
Below is the weight we assigned to each criterion. Keep it handy when you sanity-check our rankings against your own priorities.
| Criterion | Weight |
| Security & audit pedigree | 30 percent |
| Performance overhead | 25 percent |
| Integration friction | 15 percent |
| Standards alignment | 10 percent |
| Ecosystem adoption | 10 percent |
| Cost & licensing | 10 percent |
We tallied raw scores from technical papers, audit certificates, and production logs, then multiplied by these weights to reach a composite. Only the five highest totals made the cut you’re about to read.

With the ground rules clear, let’s dive into the first pick and see how it earns its spot.
#1 Project Eleven: off-chain quantum shield for any chain
Project Eleven post-quantum signing sidecar official website screenshot.
Picture a thin layer that sits in front of your blockchain node, re-signs every transaction with a NIST-approved lattice key, then hands it back as if nothing changed. That, in one sentence, is Project Eleven’s sidecar.
We like it because it tackles the hardest problem—network-wide key rotation—without asking the chain to fork. Drop the container next to your validator, point it at your wallet or custody service, and you start emitting Dilithium or Falcon signatures before lunch. Your contracts, RPC calls, and user experience stay the same, yet keys stored in consumer hardware wallets introduce a separate constraint. Project Eleven’s post-quantum hardware wallet analysis explains how secure-element devices often require new silicon for ML-DSA signatures while MCU-centric models can retrofit through firmware.
Performance was the big question until the Solana Foundation staged a public testnet in December 2025. The network pushed about three thousand transactions per second with Dilithium keys and showed no backlog in block confirmations. In other words, speed survived the surgery.
Security pedigree also checks out. Project Eleven’s codebase implements ML-DSA straight from NIST’s 2024 standard and has open-sourced its Solana testnet for public review. The team posts a public “Q-Day Clock” and backs it with a one-bitcoin bounty for anyone who can break a demo address—small but meaningful skin in the game.
Why it tops the list
- Zero protocol changes. You gain quantum safety without nudging consensus code or rewriting smart contracts.
- Enterprise-grade audit trail. Third-party reports and an active bug bounty keep the cryptography honest.
- Proven throughput. Independent benchmarks show negligible latency under high load.
- Migration runway. Because the fix lives off-chain, you can start today and move on-chain later when wallets and standards mature.
Ideal first move
If you run a lending pool, exchange, or DAO treasury on Ethereum, Solana, or any EVM chain, point Project Eleven at your hot-wallet service. You will seal today’s keys behind tomorrow’s math and buy priceless breathing room while the rest of the ecosystem catches up.
#2 PQShield: silicon-deep security for when “good enough” isn’t
![]()
PQShield quantum-safe hardware and software official homepage screenshot.
Some teams can tolerate a little overhead or opaque code. Others guard billions in value and answer to regulators who levy hefty fines. That second crowd keeps PQShield on speed-dial.
PQShield takes the heavyweight route: it bakes post-quantum algorithms directly into chips, secure elements, and hardware security modules, then surrounds that silicon with a matching software stack. By controlling the whole vertical, the company removes the usual “library in userland” attack surface and trims latency sharply. In published benchmarks, Dilithium-5 verification runs about thirty percent faster than stock OpenSSL on modern AVX2 servers, and Kyber key exchange completes in under a millisecond even under multithreaded load.
Hardware matters for side-channel resistance, too. PQShield’s IP cores are designed for FIPS 140-3 certification, complete with fault-injection and power-analysis countermeasures. That rigor is why market analysts slot the firm in the “progressive leader” quadrant of the global PQC market.
Real-world traction is growing. Hedera Hashgraph recently showcased node hardware that embeds Dilithium keys inside a secure element, the same blueprint PQShield recommends for enterprise rollouts.
Where it fits
- Institutional custody providers that need certified HSMs before moving a single satoshi.
- Central-bank pilots and CBDC platforms where compliance outweighs cost.
- Hardware-wallet vendors planning a future product cycle and unwilling to gamble on firmware patches alone.
If you are plotting a multi-year, regulator-scrutinized roadmap, PQShield’s silicon-first stance trades higher upfront spend for long-term peace of mind. Think of it as installing a vault, not just changing the locks.
#3 Open Quantum Safe: the Swiss-Army library for dev-led upgrades
Open Quantum Safe liboqs open-source post-quantum library official site screenshot.
Sometimes you do not need a turnkey service or a new layer-1 chain. You just need code—fast, flexible code you can wire into the stack you already have. That is Open Quantum Safe (OQS).
OQS ships liboqs, a C library that bundles every NIST-approved primitive plus a few experimental extras. Flip one enum and you swap Ed25519 for Dilithium. Toggle another and you are testing Kyber hybrids in TLS. The project even maintains OpenSSL and OpenSSH forks, so validators, oracles, and wallet backends can start post-quantum handshakes by swapping a shared library and restarting the service.
Breadth is the selling point. Nineteen KEMs, seventeen signature schemes, and bindings for Python, Go, Java, and Rust let your team prototype on a Friday and benchmark on Monday. That agility future-proofs you against new cryptanalytic surprises—if Dilithium ever falters, another vetted algorithm is a config change away.
There is a caveat: OQS is a kit, not a finished build. It leaves policy decisions in your hands. You must prune deprecated algorithms, enforce safe parameters, and handle key migrations carefully. For teams that enjoy working close to the metal, the pay-off is unmatched experimentation speed and no vendor ties.
Best way to use it
- Spin up a private testnet, link an OQS-enabled OpenSSL, and push real traffic through hybrid X25519 + Kyber handshakes.
- Measure block propagation, gas costs, and storage size before you commit.
- When the numbers look solid, promote the same library to staging without rewriting a single contract. That is the advantage OQS puts in your pocket.
#4 QANplatform: an EVM-compatible chain that is quantum-safe out of the box
QANplatform quantum-resistant EVM-compatible blockchain official site screenshot.
Sometimes retrofitting feels like attaching jet engines to a biplane. QANplatform avoids the patchwork entirely by starting with post-quantum signatures at genesis.
Every transaction, validator vote, and bridge message on QAN is signed with Dilithium, the same lattice algorithm the United States government standardized in 2024. No legacy keys sit under the hood, so a future quantum computer has nothing to target.
Here is the pleasant surprise: you do not surrender developer comfort to gain that security. QAN’s virtual machine speaks Solidity plus any language that compiles to Linux bytecode—Rust, Go, and Python. Port an existing dApp or build new projects in the stack your team already knows. MetaMask connects through the XLINK bridge, which quietly swaps ECDSA for Dilithium without forcing users to learn a different wallet flow.
Performance holds its own. In beta mainnet tests, blocks finalized in under five seconds, with throughput around sixteen hundred transactions per second. Those numbers match today’s high-speed chains, minus the quantum risk.
When QAN shines
- New DeFi projects that plan to lock value for years and do not want a future key-migration scramble.
- Enterprise consortia that need private instances today but public settlement tomorrow; QAN’s hybrid approach lets you run both.
- Communities that want an insurance policy if Ethereum’s migration stalls; bridge assets over, stay EVM-friendly, and sleep better.
If Project Eleven is a bolt-on shield and OQS is a toolkit, QAN is the fresh concrete foundation. Build once, build future-proof.
#5 Algorand: a major chain proving PQC works in production

Algorand blockchain with Falcon-1024 post-quantum state proofs official website screenshot.
Big-cap blockchains rarely move quickly, yet Algorand already signs part of its consensus with Falcon-1024. The network reached that milestone on November 3, 2025, executing the first Falcon-secured state proof on mainnet while still pushing ten thousand transactions per second. The result shows that quantum safety and performance can coexist.
Right now, everyday transfers still ride Ed25519. That is by design. The core team chose a gradual, opt-in path: advanced users can generate Falcon keys through the command line, dApps can verify those signatures in the next AVM upgrade, and the rest of the ecosystem continues uninterrupted. It is a living case study in how to migrate without igniting a governance fire.
Why include a “partial” solution in a top-five list? Scale matters. When a chain with billions in total value and a global developer base proves PQC in the wild, the rest of the industry pays attention. Algorand’s progress buys every participant a longer runway before a forced, last-minute fork.
Where Algorand fits
- Teams that want a mature DeFi ecosystem today and a clear, scheduled path to quantum safety tomorrow.
- Cross-chain builders who need quantum-secure proofs when bridging assets or data.
- Long-horizon projects—such as bond markets or insurance pools—that demand evidence a chain can evolve without breaking user experience.
If you need the credibility of a mainstream network plus steady progress toward post-quantum security, Algorand offers the best of both worlds.
Quick-glance comparison table.
Choosing a solution is simpler when the facts sit side by side. Scan the grid below, then zero in on the row that matches your risk profile and engineering capacity.
| Solution | Primary approach | PQC algorithms | Integration effort | Performance hit | Notable deployment | Our score |
| Project Eleven | Off-chain signing sidecar | Dilithium & Falcon | Low – plug-in endpoint | None on chain | Solana 3 000 TPS testnet | 5/5 |
| PQShield | Software plus hardware IP | Dilithium, Kyber, Falcon | High – chip / HSM integration | Negligible with silicon assist | Hedera node hardware | 5/5 |
| Open Quantum Safe | Open-source library | All NIST PQC suites | Medium – dev led | Moderate (larger payloads) | Used in Cloudflare prototypes | 4/5 |
| QANplatform | Dilithium native L1 | Dilithium (FIPS 204) | Low for EVM teams | Low – 1 600 TPS beta | MetaMask XLINK demo | 4/5 |
| Algorand | Mainnet hybrid rollout | Falcon-1024 (state proofs) | Low – opt-in keys | None for state proofs | First Falcon transaction Nov 3 2025 | 4/5 |
Use the table as a filter, not a verdict. If you need instant coverage without touching core code, Project Eleven leads. If auditors require hardware attestations, PQShield takes the front seat. And if you want a brand-new chain that still speaks Solidity, QANplatform is ready.
Implementation checklist: from whiteboard to mainnet
A shiny roadmap means nothing if the upgrade stalls in testing. Work through these steps in order, checking each box before you advance.
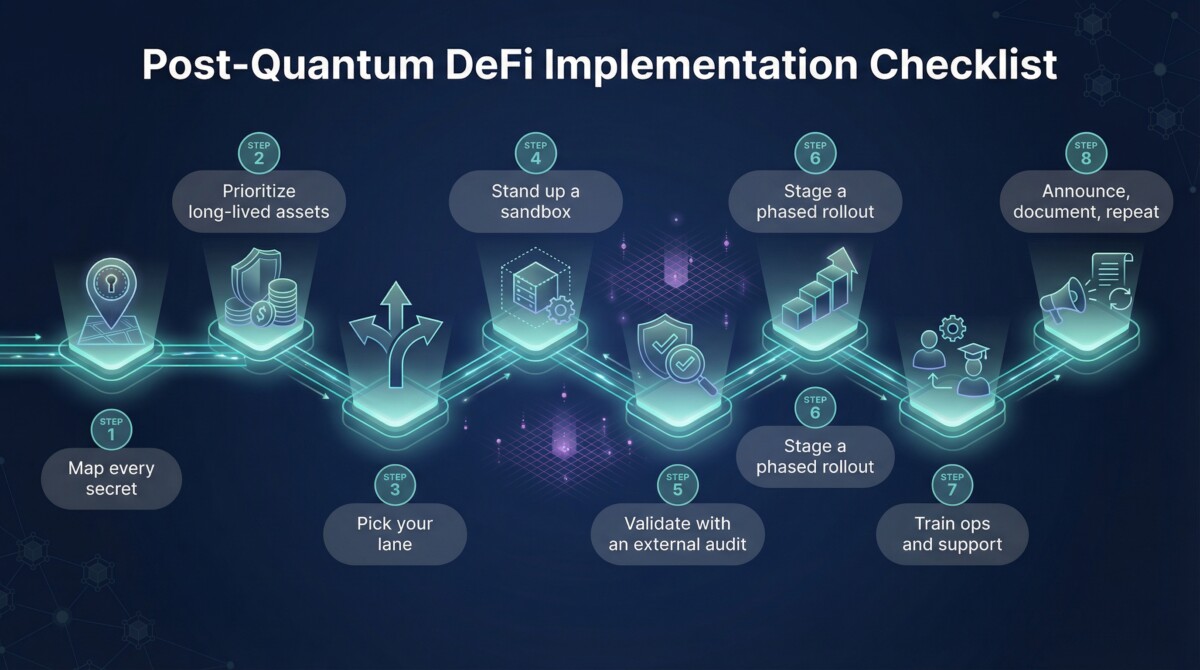
- Map every secret.
List where keys live today: validator nodes, hot wallets, cold storage, contract admin roles, off-chain oracles. Until you see the full impact you cannot triage the fix. - Prioritize long-lived assets.
Governance multisigs, treasury wallets, and bridge contracts hold value for years. Harden those first; trading keys that rotate daily can wait a sprint. - Pick your lane.
Choose a bolt-on shield, a library swap, or a new chain. That decision drives hardware budgets, audit scope, and community messaging. - Stand up a sandbox.
Clone production configs into a private network. Add your chosen PQC tooling and push real traffic through it. Watch for signature size, gas bumps, or TLS surprises. - Validate with an external audit.
Fresh cryptography deserves fresh eyes. Hand the testnet to an independent firm and fix anything they flag before mainnet headlines appear. - Stage a phased rollout.
Start with cold storage, then custody workflows, then live wallets. Keep classical and quantum keys side by side until the new path proves stable. - Train ops and support.
Larger keys affect signing latency, backup scripts, and even QR-code sizes. Make sure human processes grow with the math. - Announce, document, repeat.
Publish what changed, why it matters, and how users verify the new signatures. Transparency turns potential panic into goodwill.
Conclusion
Adopting post-quantum cryptography today turns a looming existential threat into a strategic advantage. Use the rankings, comparison table, and checklist above to chart a clear, accountable path to quantum-safe DeFi operations.
Frequently Asked Questions
How urgent is post-quantum migration for a DeFi protocol that is live today?
The urgency depends on two factors: how long your assets will be at risk and how long your migration will take. NIST finalized ML-DSA and SLH-DSA in 2024, which means the standards are no longer a moving target. Harvest-now-decrypt-later attacks are already happening, where adversaries archive encrypted data and public keys today to break them once a cryptographically relevant quantum computer exists. Estimates for that threshold range from five to fifteen years depending on which research team you ask. If your protocol manages assets that will still have value in that window, and most DeFi protocols do, the migration clock is already running. The teams that start now control the timeline. The teams that wait will execute under pressure with fewer options.
What is the difference between ML-DSA and Falcon and which should my DeFi protocol use?
Both are lattice-based signature schemes standardized by NIST, but they make different tradeoffs. ML-DSA, formerly Dilithium, produces larger signatures around 2.4 kilobytes but is simpler to implement correctly and has a broader software support ecosystem. Falcon produces much smaller signatures around 666 bytes for Falcon-512 but is significantly harder to implement safely due to floating-point arithmetic requirements that introduce subtle side-channel risks if not handled carefully. For most DeFi protocols starting a post-quantum migration today, ML-DSA is the lower-risk choice because the implementation complexity is manageable and the tooling is more mature. Falcon makes sense when signature size is a hard constraint, such as in state proof systems or high-frequency on-chain verification contexts where byte costs directly affect gas fees.
Can I add post-quantum signatures to an existing Ethereum smart contract without a protocol upgrade?
Yes, and Project Eleven’s off-chain sidecar architecture is specifically designed for this use case. The approach intercepts transactions at the wallet or custody layer, re-signs them with a Dilithium or Falcon key, and submits them to the chain without modifying any smart contract logic or consensus rules. This works today on any EVM-compatible chain. The limitation is that the quantum-safe signature lives off-chain. The on-chain record still uses ECDSA. For full on-chain quantum safety, you need either a protocol upgrade that recognizes post-quantum signature schemes in the EVM, or a chain like QANplatform that was built with Dilithium at the consensus layer from genesis. The off-chain approach buys time and protects custody workflows immediately. Full on-chain safety requires a longer migration path.
How much does post-quantum migration increase transaction costs and storage requirements?
The overhead is real but manageable with the right approach. ML-DSA signatures are approximately 50 times larger than ECDSA signatures. A standard ECDSA signature is 64 bytes. A Dilithium-3 signature is roughly 3.3 kilobytes. On chains that charge gas per byte of calldata, that size difference translates directly into higher transaction costs. Algorand’s state proof approach sidesteps this problem by using Falcon signatures only for periodic consensus checkpoints rather than every transaction, keeping per-transaction costs unchanged. For protocols where every transaction carries a post-quantum signature, the practical answer is to benchmark your specific transaction mix on a testnet and model the cost impact before committing to a signature scheme. Some protocols absorb the overhead. Others redesign their signing architecture to minimize on-chain signature footprint.
What should I do first if my team has no prior post-quantum experience?
Start with the Open Quantum Safe library on a private testnet. It costs nothing, requires no vendor relationship, and gives your engineers direct hands-on exposure to every NIST-approved algorithm in a controlled environment. Spend two weeks running your existing transaction load through hybrid X25519 plus Kyber handshakes and measuring the real performance impact on your specific stack. That exercise will answer 80% of your team’s open questions about signature sizes, key management overhead, and library integration complexity. From there you will have enough concrete data to make an informed choice between the five solutions covered here. The worst thing you can do is make an architectural commitment based entirely on vendor benchmarks and white papers without any direct experimentation against your own infrastructure.