
Welcome to Rewind’s first edition of the Backup Brief, your monthly round-up of what’s making cybersecurity news this month. Here’s what our cybersecurity experts have been talking about this month:
A cybersecurity incident that took down the website of Indigo Books & Music Inc. continued for more than one week, just the latest in a string of attacks on Canadian organizations and an example of a growing concern across the retail industry. Indigo has confirmed that the ransomware attack exposed past and current employee information, although they maintain that no customer data was leaked.
Indigo would not comment on how much money it has lost, but it’s predicted to be at least millions of dollars, if not tens of millions, said Bruce Winder, retail analyst and author.
After an outage of 10 days (and a temporary browse-only site), Indigo.ca is now back online after partnering with Shopify to relaunch their store in just three days (our kudos to the hardworking devs of Shopify). Of course, if they had a reliable recovery solution for their store data like Rewind Backups for Shopify, store restoration could’ve been accomplished in hours, not days.

Despite the company’s dedication to transparency during this outage, Indigo’s brand reputation is likely suffering, as today’s consumers are extremely picky about ecommerce site functionality. Recent research has found 88% of consumers are less likely to return to a site after a single bad experience, further highlighting that there are no second chances on the internet.
Enterprise software giant Atlassian has launched an investigation after a hacker group leaked information belonging to the company. A threat actor named SiegedSec, whose members have claimed to be hacktivists announced on its Telegram channel and hacking forums that it “hacked the software company Atlassian.”
Late on Valentine’s Day, they made 35 Mb of files public. This includes two image files apparently storing floor plans of Atlassian buildings in San Francisco and Sydney, and one file allegedly containing the information of 13,000 Atlassian employees, including names, email addresses, and phone numbers.
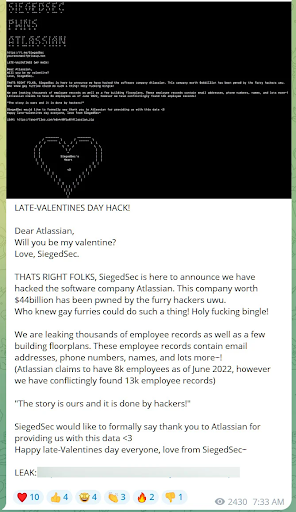
The hacking group had managed to obtain “an Atlassian employee’s credentials that had been mistakenly posted in a public repository by the employee.” If you needed another reminder to never hardcode your credentials, this is it.
The hacking group had managed to obtain “an Atlassian employee’s credentials that had been mistakenly posted in a public repository by the employee.” If you needed another reminder to never hardcode your credentials, this is it.
Reddit has confirmed that the social media company suffered a data breach on February 5. “After successfully obtaining a single employee’s credentials,” Reddit CTO Christopher Slowe explained in a recent statement regarding the attack, “the attacker gained access to some internal docs, code, as well as some internal dashboards and business systems.”
Slowe said that Reddit’s systems show “no indications of a breach of our primary production systems (the parts of our stack that run Reddit and store the majority of our data)” but did confirm that “limited contact information… for company contacts and employees (current and former), as well as limited advertiser information” were all accessed.
At present, Reddit has “no evidence to suggest that any of your non-public data has been accessed, or that Reddit’s information has been published or distributed online.”
Yet another example of why multi-factor authentication (or better yet, a security key) is essential in today’s cyberthreat landscape.
Healthcare companies (and anyone storing lots of valuable PII, like health insurance records) are a longtime favorite of hackers, and this month was no exception.
Sharp HealthCare, which is the largest healthcare provider in San Diego, California, has notified nearly 63,000 patients that their personal information was exposed during a recent attack on the organization’s website. Social Security numbers, health insurance data, and health records belonging to customers have all been compromised, but Sharp says no bank account or credit card information was stolen.
Sharp says the type of compromised information “varied from person to person,” which is concerning for users who may have had their PII leaked. Cybercriminals can use leaked credentials like social security numbers and health records to create more convincing scams; people are often more susceptible to interacting with scams that include some of their (thought-to-be) private information. There’s a reason healthcare is referred to as a “prized ticket” for cyber scammers and criminals.
As the 2023 annual meeting of the World Economic Forum wrapped up in Davos, Switzerland, it ended with a disturbing prediction from one of the leading voices. Delivering a presentation on the 2023 Global Cybersecurity Outlook report, forum Managing Director Jeremy Jurgens revealed that 93 percent of those surveyed believe that a “catastrophic” cyber security event is likely in the next two years.
By 2025, it’s expected that cybercrime will cost the world economy around $10.5 trillion annually, increasing from $3 trillion in 2015 according to Cybersecurity Ventures. To put that in context, if it were a country, cybercrime would have the third largest GDP behind the US and China. Key drivers of this growth are the ongoing digitization of society, behavioral changes due to the global Covid-19 pandemic, political instability such as the war in Ukraine, and the global economic downturn.
Sadly, there’s no shortage of cyberthreats in today’s cloud-first, SaaS-dependent ecosystem. That’s why an account-level backup and recovery system of your personal data is an essential part of a solid disaster recovery plan. Don’t find out about the devasting effects of data loss via personal experience; prepare now by backing up your business-critical data with Rewind.